Summary: Powerline adaptors are better than they used to be but they aren’t without their problems.
Summary: Powerline adaptors are better than they used to be but they aren’t without their problems.
I’ve recently moved house and didn’t want to go to the time and expense of wiring up my new house with CAT6 ethernet, so opted for some Powerline adapters instead. I’d used an early set of these (85Mbps) back in 2007 but standards have definitely advanced in this area and now we have 500Mbps adapters (well sort of) so I thought it was worth revisiting the technology.
My local computer store had a couple of TP-Link units in stock (WPA4220 Starter Kit) and I bought them on a whim. Plugging them in and getting them working took all of five minutes and voila – connectivity! The speeds weren’t great (around 80Mbps on average, so 5-6MBps on file transfers) but then my house was built in the 70s so it’s not especially modern and that does affect speeds. The bigger variable in my case was the fact I have a three phase power supply, rather than the more usual one. At first I thought this would prevent or greatly hinder my use of powerline networking but my powerline networking works just fine over multiple power phases (apparently a shared consumer unit is key). Speed is affected (my dropped to 60Mbps when crossing phases) but I’m really just using it for web browsing and streaming some video which seems to work fine.
UPDATE APRIL 2015 – I’ve now done some testing with iPerf and my speeds are lower than those reported by the TP-Link utility – often significantly. For example TP-Link reports 75Mbps when iPerf reports 25Mbps for the same link. Even allowing for protocol overheads there’s a significant discrepancy. I think TP-Link may be reporting ‘theoretical’ speeds achievable over my powerlines (using the PHY layer) whereas ‘real world’ transmission is impacted by many other factors. Still, I can stream HD without issue most of the time.
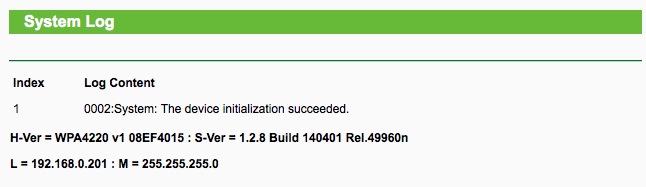
All said I was very happy with my powerline setup, until I’d been running the integrated wireless AP for a few days and started noticing connectivity problems. I’ve got a mixture of tablets (a couple of iPads, Nexus 7), smartphones, Sonos wireless speakers and the odd Google Chromecast and found that within a day or so they’d lose internet access. After further investigation and some Googling I found plenty of people in a similar scenario (here, here, here, and here) but with no acknowledgement or fix forthcoming from TP-Link. Sadly the logs for these units are hardly worth having as you can see in the screenshot below – over 20 hours after powering it on (and with Wifi failing) all that was logged was the initial startup event and even that didn’t have a timestamp;
The problem seems to be certain types of traffic don’t pass through the wireless AP, even through plugging into the wired http://premier-pharmacy.com/product/abilify/ powerline socket on the same unit works fine. I quickly identified that DHCP broadcasts weren’t being received by wireless clients so devices were failing to renew their leases and dropping off the network. A simple reboot of the TP-Link resolves the issue for a while but it recurs within a few hours. Interestingly setting a static IP seems to be a good partial workaround as the wireless AP is still working and sending most types of traffic, but some devices, like the Chromecast, only support DHCP. For my Chromecast I’ve therefore set my DHCP server to reserve an IP for about a year! To alleviate the issue even further I’ve now bought a mains timer switch and automatically reboot the unit twice a day – a horrible hack, but it works. When the wireless fails I can’t even ping the TP-Link’s IP address wirelessly, even though i can ping my router and other devices on my network, and I can ping the TP-Link via a wired connection. Frustrating.
Without much visibility under the hood (this can’t run the highly customisable DD-WRT as that doesn’t understand powerline networking) the best I can tell is that some types of traffic are not being bridged onto the wireless AP correctly. I’m sure a few Wireshark captures would confirm this in more detail but as I’m relying on TP-Link to fix it one way or another I haven’t drilled down to that level. Unfortunately I believe a software fix (ie firmware update) is required and so far nothing has been forthcoming from TP-Link. On one of the posts linked to above there’s a post from ‘Vincent’, who I believe works for TP-Link, claiming that they’re trying to replicate the issue – I’m not sure why that should be difficult as I’d imagine a software issue would be pretty consistent but I can give them the benefit of the doubt for a while longer. Judging by a blogpost from Alex Boschman it looks like the equivalent Devolo unit’s aren’t immune to problems either, so maybe I’ll have to try D-Link or Solwise instead. Or maybe I’ll just wire up the house after all and use a standard wireless device, it might still be the most quickest way to get reliable access… 🙁
UPDATE: 27th November – I’ve now also tried a TP-Link TL-WPA281 which is essentially the older variant which only offers 300Mbps for the wireless AP. Sadly this behaves the same way. I’ve also experimented replacing the wireless functionality of the TP-Link with an old Netgear unit (WGR614v9) (I plug the Netgear into the TP-Link, so I’m still using the powerline aspect) and that seems to work flawlessly so I still think the TP-Link devices are the cause of my wifi issues.
Further Reading
Google chromecast network traffic (via Cisco)